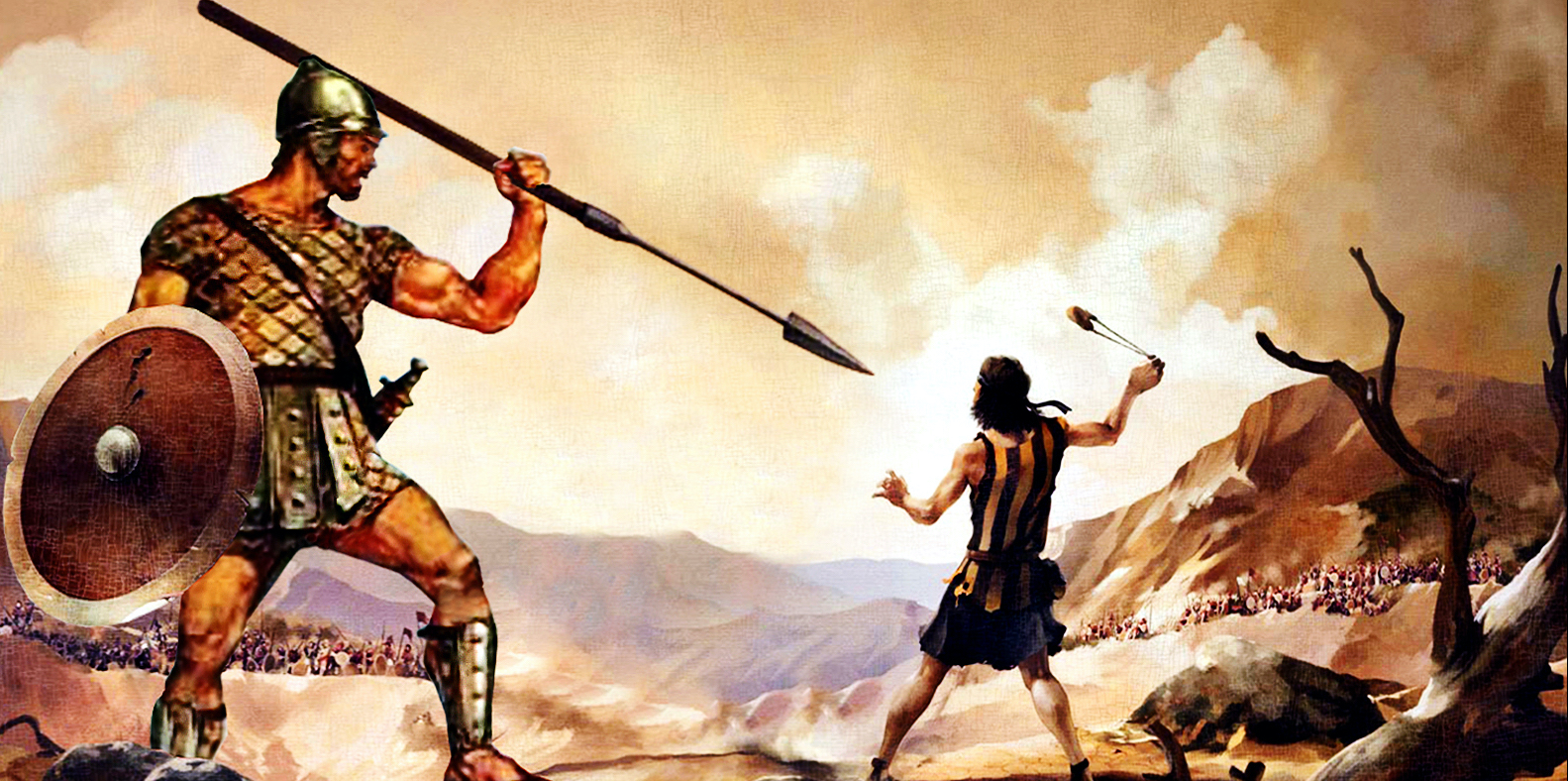
Twitter Hack Reminds Us That David Can Still Fell Goliath
The twitter hack began as a quiet scheme to steal and sell unusual user names, which carry high currency in gamer and hacker circles.
But as the day wore on, the attack took over dozens of accounts belonging to corporations like Apple and celebrities like Joe Biden, Barack Obama, Bill Gates, Elon Musk and Kanye West. The hackers used the celebrity access to appeal to their followers for funds:
 At least $180,000 worth of Bitcoin flowed into the hackers’ accounts.
At least $180,000 worth of Bitcoin flowed into the hackers’ accounts.
By the time the hackers were done, they had broken into 130 accounts and dramatically exposed gaping holes in Twitter’s security.
What organized Goliath cybercrime ring was responsible?
Seventeen-year-old Florida resident, Graham Ivan Clark (David, for the purpose of this metaphor).
From the affidavit:
Graham Ivan Clark, 17 without authorization gain [sic] access to Twitter Inc.’s Customer Service Portal. Clark used social engineering to convince a Twitter employee that he was a co-worker in the IT department and had the employee provide credentials to access the customer service portal.
Clark then accessed the Twitter accounts of prominent individuals, including VP Joe Biden, former President Barack Obama and business [sic] such as Apple and Coinbase. Clark then posted on their Twitter accounts a communication that if Bitcoins are sent to accounts they will be doubled and returned to the victim.
Despite the hackers’ cleverness, their plan quickly fell apart, according to court documents. They left hints about their real identities and scrambled to hide the money they’d made once the hack became public. Their mistakes allowed law enforcement to quickly track them down.
If Twitter, a company that spends millions on security ever year, can be hacked by a 17-year-old, so can your organization. But it wasn’t the technology that was hacked, it was the people.
It is no surprise that the twitter hackers used the same tool that leads to a majority of damaging corporate breaches: social engineering. Twitter says that a few employees were targeted in a phone spear phishing attack, which suggests that hackers called Twitter employees while posing as members of the Twitter’s security team, and got them to reveal the credentials they use to access internal systems.
Once inside the system, they had free rein to do anything they wanted with any Twitter account. The next time this breach happens, the criminals will be more organized, and will use their access to launch a much more devious, lucrative scheme.
I hope Twitter invests as readily in their security awareness training and social engineering defenses as they do on their technology. And I hope you do as well, as it’s no fun to be beaten by David.
![]() John Sileo is a cybersecurity expert, award-winning author and media personality as seen on 60 Minutes, Anderson Cooper and Fox & Friends. He keynotes conferences virtually and around the world and is the CEO of The Sileo Group, a technology think tank based in Colorado.
John Sileo is a cybersecurity expert, award-winning author and media personality as seen on 60 Minutes, Anderson Cooper and Fox & Friends. He keynotes conferences virtually and around the world and is the CEO of The Sileo Group, a technology think tank based in Colorado.