Cybersecurity Alert: UnitedHealth’s Billion Dollar Data Breach
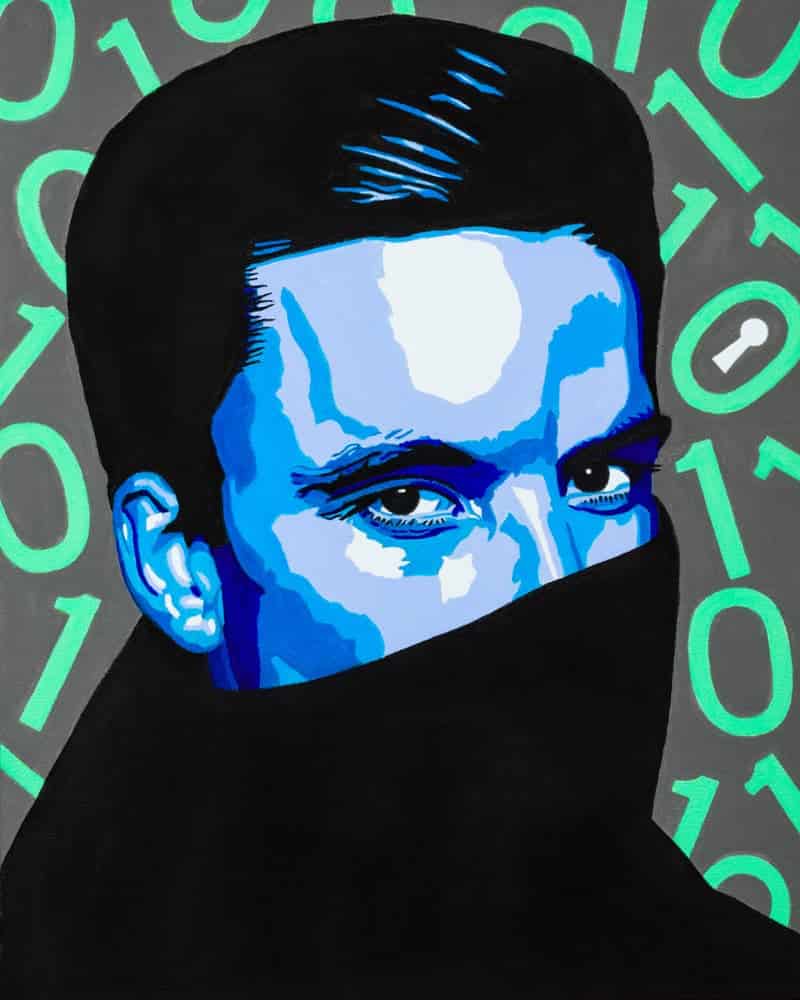
One in three Americans recently had their healthcare data hacked from UnitedHealth – TWICE. The stolen data likely includes medical and dental records, insurance details, Social Security numbers, email addresses and patient payment information.
UnitedHealth Group’s subsidiary, Change Healthcare (which processes an estimated 50% of all health insurance transactions in the U.S.), fell victim to a ransomware attack that thrust the U.S. healthcare system into chaos as pharmacies, doctor’s offices, hospitals and other medical facilities were forced to move some operations to pen and paper.
Behind the scenes, UnitedHealth Group chose to pay the BlackCat ransomware gang (aka ALPHV) an estimated $22 million in blackmail ransom to restore system functionality and minimize any further leakage of patient data.
Problem (expensively) solved, right? Not even close. After UnitedHealth paid the initial ransom, the company (or quite possibly BlackCat itself being hacked by hackers) reportedly experienced a second attack at the hands of RansomHub, which allegedly stole 4TB of related information, including financial data and healthcare data on active-duty U.S. military personnel.
To take the breach and ransom to an entirely new level, RansomHub is now blackmailing individual companies who have worked with Change Healthcare to keep their portion of the breached data from being exposed publicly. For many small providers, the ransom is far beyond what they can afford, threatening the viability of their business. Some of the larger individual providers being blackmailed are CVS Caremark, MetLife, Davis Vision, Health Net, and Teachers Health Trust.
As of today, even with millions of dollars collected by the hackers, all systems are not up and running.
There are three critical business lessons to take from the UnitedHealth breach:
- Ransom payments do not equal the cost of breach. The ransom amount companies pay is a fraction of the total cost of breach. In UnitedHealth’s case, they paid a first ransom of $22 million, but only months into the breach have reported more than $872 million in losses. Operational downtime, stock depreciation, reputational damage, systems disinfection, customer identity monitoring, class action lawsuits, and legal fees will move the needle well beyond $1 billion within the fiscal quarter. Risk instruments like cyber liability insurance can balance the losses, but prevention is far more cost-effective.
- There is no honor among thieves. Even when organizations pay the ransom demanded, (and in the rare case that they get their data back fully intact), there is no guarantee that the cybercriminals won’t subsequently expose samples of the data to extort a second ransom. In this case of Double-Dip Ransomware (as I call it), a dispute among partnering ransomware gangs meant that multiple crime rings possessed the same patient data, leaving UnitedHealth open to multiple cases of extortion. Paying the ransom instead of having preventative recovery tools places a larger target on your back for future attacks. If you haven’t implemented AND tested a 3-2-1 data backup plan and a Ransomware Response Plan, do so immediately.
- The Human Hypothesis on the Source of Breach. There has been no disclosure to date on exactly how the hackers got into Choice Health’s systems, but my highly educated guess (from seeing so many similar breaches) is that an employee of, or third-party vendor to, UnitedHealth was socially engineered (scammed) to share access into one of their business IT systems. The company will generally report this human oversight and poor training as “compromised credentials” which tries to make it look like a technological failure rather than a human decision. From there, the hackers “island hopped” laterally to increasingly critical servers on the network. It’s likely that the cyber criminals are still inside of key systems, hiding behind sophisticated invisibility cloaks.
The solution here is to make sure that the heroes in your organization, the human employees who are your first and best line of defense, are properly trained on how to detect and repeal the latest social engineering attacks. Over 90% of all successful attacks we see are due to a human decision that leads to malicious access.
All organizations and leadership teams must ensure your Security Awareness Training addresses all the changes that artificial intelligence brings to the cyberthreat sphere. To ignore the alarm bells set off by UnitedHealth Group’s disastrous breach is to risk your organization falling ill to a similar fate.
Anyone in your organization can be the unfortunate catalyst that triggers a disastrous data breach similar to UnitedHealth’s. My latest keynote, Savvy Cybersecurity in a World of Weaponized A.I., teaches the root cause of successful social engineering scams and necessary technological preparation for ransomware attacks. REACH OUT TO MY TEAM TODAY to discuss this vital topic at your next meeting or event.
- If you are a patient of UnitedHealth, Change Healthcare, OptumRx or any of their subsidiaries, take the following steps immediately:
- Visit the Cyberattack Support Website that UnitedHealth Group established for affected customers.
- Make sure that you have a Credit Freeze on your Social Security Number.
- If you are an OptumRX customer, call them directly (1-800-356-3477) to make sure that your prescriptions haven’t been affected and that they will ship on time.
- Monitor all of your health and financial accounts closely for any changes or transactions. Create automatic account alerts to make this easier.
John Sileo is a privacy keynote speaker, award-winning author and media personality as seen all over TV. He keynotes conferences virtually and in person around the world. John is the CEO of The Sileo Group, a business think tank based in Colorado.