The Unlikely Weapon in Cybersecurity: Going Analog
Rule #1: Technology is highly unpredictable when it’s new & untested. And even worse when it’s insecure.
All of us have learned not to count on Technology Version 1.0 in mission critical situations. But it seems that Iowa and Pennsylvania didn’t get the memo, which rendered their election results as untrustworthy. Iowa attempted to use a caucus tally app that had very few cybersecurity protections and hadn’t been adequately tested prior to caucus night. Combined with an earlier voting fiasco in Pennsylvania, it’s logical to conclude that the only way to ensure the integrity of our elections is to use paper ballots.
As if Iowa didn’t make it clear enough, a recent voting fiasco in Pennsylvania was a stark reminder that the only way to ensure the integrity of our elections is to use paper ballots, either as a primary means or in a backup role. In Northampton County, a glitch in the computer voting system resulted in some straight-line Democrat votes being recorded as straight-line Republican, and gave a statistically impossible victory to a Republican judicial candidate. Thanks to paper backups of the electronic ballots, election officials were able to do a manual recount and restore the actual election results (the Republican judicial candidate lost by a small margin).
As The Washington Post reported, voters got lucky. The margin of victory for the Republican candidate was so massive that there was obviously something wrong, but what if the margin has been in the probable range? It’s likely the error would never have been uncovered.
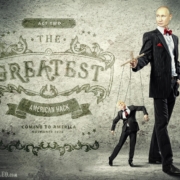
The Northampton County voting machines were recently purchased in response to last February’s state-wide mandate to adopt voting systems with paper back-ups before the 2020 elections. In making the move, Pennsylvania joined other states in upgrading or replacing voting systems following Russian interference in the 2016 election and warnings from “ethical hackers” that voting machines in the U.S. are vulnerable.
Recently, Colorado became the first state to ban barcodes for counting votes, opting instead for receipts that show darkened ovals identical to the ballot itself. Colorado is also one of a handful of states to aggressively emphasize mail-in ballots, both for convenience and security’s sake. These moves come amid growing concerns over election security following Russian interference in the 2016 election and warnings from “ethical hackers” that voting machines in the U.S. are vulnerable.
Reintroducing selective physical and human elements into the technological supply chain is the best weapon we have to protect our elections from interference. But this strategy—going analog—shouldn’t be limited to voting machines; it needs to be implemented across the board in public and private enterprise.
In our zeal to embrace the digital revolution and the convenience of smart devices, we’ve sacrificed some security, not to mention privacy. It’s hard to name a product or service that isn’t networked, but connecting every known device to the internet doesn’t necessarily make us “smart.” It makes us vulnerable. From Siri and Alexa to our televisions, insulin pumps and even refrigerators, our lives are increasingly dominated by digital tech—which is not only sharing our data but can also be hacked and manipulated.
In July, the Department of Homeland Security issued a security alert, warning that flight systems of small aircraft can be easily and quickly hacked by someone with physical access to the plane. And last month, hackers successfully sabotaged vital systems of an F-15 fighter jet during an Air Force-sanctioned experiment at Def Con.
The Def Con operation represents an increasing willingness of government agencies to open their doors to ethical hackers in an effort to thwart rising cybercrime. In August, 22 Texas towns were hit by a coordinated attack, in which computer systems were taken over and held for ransom. And that was hardly an isolated incident; Baltimore, Riviera Beach and a host of cities were similarly hit. According to CBS, 50 of 70 U.S. ransomware attacks in the first half of the year targeted cities.
Even more troubling, an April report by the Ponemon Institute, found that 90% of all critical infrastructure providers say their Information Technology (IT) and Operational Technology (OT) environments have been damaged by a cyberattack in the last two years, and 62% experienced two or more attacks. Operational technology is what runs the physical systems behind our planes, trains, ships, traffic systems and power grid—so the stakes have skyrocketed from lost data to lost lives.
As cybercriminals ramp up attacks on Critical National Infrastructure (CNI), it’s vital that we innovate beyond increasingly ineffective cybersecurity measures. Thanks to mobile devices, the Internet of Things and cloud computing, “securing the perimeter” is no longer achievable.
The fact is, once information or operational systems are digitized, they are vulnerable to attack by remote forces—including hostile nation states, organized crime and malicious competitors. In other words, when the only method of controlling a system is digital, hackers have a way to assume 100% control. Going analog—introducing human and physical “backstops”—provides our best defense against network-based remote control.
For example, commercial and private aircraft should be equipped with an “override” analog system that allows the pilot to disconnect the plane in the event of an attack and control it manually. The same is true for gas and electric utilities, traffic systems, hospitals and maybe even corporate computer networks.
The U.S. Navy was an early adopter of the human solution, bringing back celestial navigation training in 2015. The move to train recruits and officers in the ancient art of navigating by the stars was prompted in part by fears that the Global Positioning System (GPS) satellites could be shot down, or the system simply hacked or jammed. It was a prudent decision, given that cheap GPS jammers can easily be found online.
Meanwhile, that same year, the Ukranian power grid was digitally attacked by Russia—leaving 225,000 customers in the dark. Grid operators on the ground were able to physically override digital systems to get the power back on in a reasonable time.
These two examples illustrate a key point: Just because systems or techniques were used in the “old days” or aren’t connected to the internet, doesn’t mean we should exclude them as part of the security equation. We haven’t given up seatbelts just because smart cars automatically brake to prevent a collision. We should apply that same “both/and” logic to cybersecurity: The solutions can and should be both technological and human, digital and physical, internet-connected and old school.
That’s the thinking behind the Securing Energy Infrastructure Act (SEIA), introduced in the Senate in 2016 (following the Ukranian attack).
The press release announcing the Senate’s passage of the SEIA earlier this summer stated that the act aims to remove vulnerabilities that could allow hackers digital access to the energy grid, and “replace automated systems with low-tech redundancies, like manual procedures controlled by human operators.” SEIA is currently being considered in the House as part of the National Defense Authorization Act for Fiscal Year 2020. If it passes, a two-year pilot program will be set up to identify vulnerabilities and test analog solutions.
While the SEIA winds its way through Congress, the private sector is already implementing analog solutions. In my work with defense contractors, I’ve seen entire computer systems taken permanently offline to keep them out of reach of remote foreign actors (to avoid situations such as China’s theft of Lockheed Martin’s plans for the F-35 fighter jet). This technique, known as air-gapping is not perfect, but it does make digital espionage more difficult. Similarly, classified communications often take place face-to-face—even when it requires travel to meet in person—and I’ve been in highly confidential meetings where the chosen “recording” devices were a whiteboard, dry-erase markers and the human brain.
Many corporations are limiting what data they digitize in the first place, selectively opting to archive paper documents and records with physical locks rather than risk a remote hack. I’ve worked with several food-industry clients that have taken their recipe for the “secret sauce” completely offline, choosing to protect their intellectual property using nondigital means. It’s exponentially harder to gain access into a confidential physical location—especially when access is limited to a small group of trusted users.
Even small businesses can benefit by taking key systems offline overnight, when a majority of successful hack attempts take place. Imagine the lawyer, dentist or doctor that eliminates more than 50% of all hacking attempts simply by shutting down their internet connection before they leave the office. This doesn’t work if employees are working remotely or data backups take place overnight, but many smaller businesses go offline at closing time.
I’m not saying that all data should be handled this way or that (God forbid) we return to rotary phones—in fact, I’m a believer in the positive power of big data and the smart use of technology to drive progress and innovation. However, in the absence of a 100% foolproof method of protecting the digital systems that we rely on—including those responsible for our safety and security—we need to add analog protection on a selective, well-planned basis.
True innovation isn’t just adopting the latest technology. It’s also knowing how to beat it.
About Cybersecurity Keynote Speaker John Sileo
John Sileo is the founder and CEO of The Sileo Group, a privacy and cybersecurity think tank, in Lakewood, Colorado, and an award-winning author, keynote speaker, and expert on technology, cybersecurity and tech/life balance.


 Sileo.com
Sileo.com 

 Sileo.com
Sileo.com sileo.com
sileo.com